Caller Alert Documentation Linked With 18003470350 and Logs
Caller alert documentation linked with the number 18003470350 serves as a critical resource for organizations aiming to enhance communication security. By analyzing call logs, patterns indicative of potential fraud can be discerned. This systematic approach not only protects sensitive information but also reinforces trust in communication practices. As organizations implement these strategies, understanding the implications of such documentation becomes increasingly essential for optimizing operational efficiency. What specific patterns might emerge from these logs?
Importance of Caller Alert Documentation
The significance of Caller Alert Documentation lies in its role as a critical tool for enhancing communication efficacy within organizations.
By ensuring documentation accuracy, organizations can maintain caller privacy while effectively managing interactions.
This meticulous record-keeping fosters trust and transparency, allowing for informed decision-making.
Ultimately, accurate caller documentation empowers teams to optimize their workflows and respond to inquiries with greater precision and confidence.
Security Enhancements Through Caller Alerts
While organizations prioritize effective communication, the integration of Caller Alerts significantly enhances security measures.
This system enables caller verification, establishing authenticity and mitigating risks associated with impersonation. By incorporating advanced algorithms, Caller Alerts serve as a robust tool for fraud prevention, ensuring that organizations can confidently engage with verified contacts.
Thus, security protocols are strengthened, fostering an environment of trust and reliability in communications.
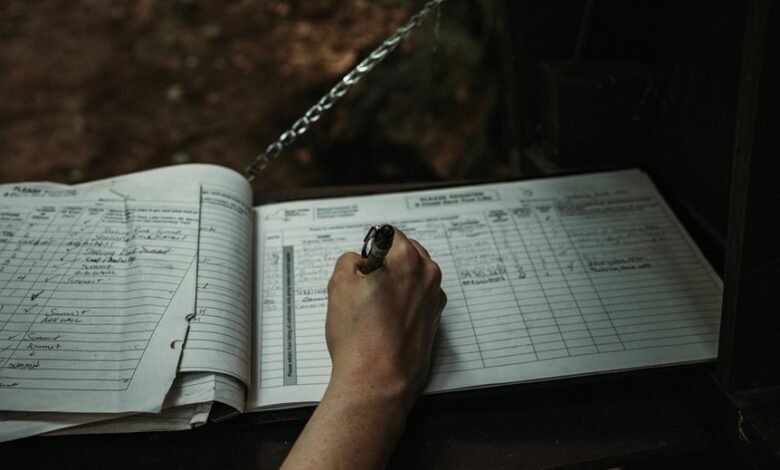
Analyzing Call Logs Associated With 18003470350
When analyzing call logs associated with the number 18003470350, it is essential to identify patterns and anomalies that may indicate fraudulent activity or unauthorized access.
Call log analysis must prioritize data privacy to ensure that sensitive information remains protected. By systematically reviewing call durations, frequencies, and originating numbers, one can uncover potential risks while maintaining the integrity of personal data.
Practical Applications for Businesses and Individuals
Call log analysis offers valuable insights for both businesses and individuals, facilitating informed decision-making and enhancing security measures.
By utilizing caller identification technologies, organizations can streamline efficient communication, ensuring that critical calls are prioritized.
Individuals benefit by recognizing potential threats, thereby safeguarding personal information.
Ultimately, the strategic application of call log data empowers users, promoting autonomy and informed choices in their communication practices.
Conclusion
In conclusion, the meticulous documentation of caller alerts linked to 18003470350 is not merely beneficial; it is a revolutionary cornerstone in communication security. By scrutinizing call logs with surgical precision, organizations can unveil a universe of insights, thwarting fraudulent activities with an unmatched vigilance. This proactive stance is not just about safeguarding information; it elevates trust to stratospheric heights, transforming the very fabric of corporate communication into an impenetrable fortress of transparency and efficiency.





